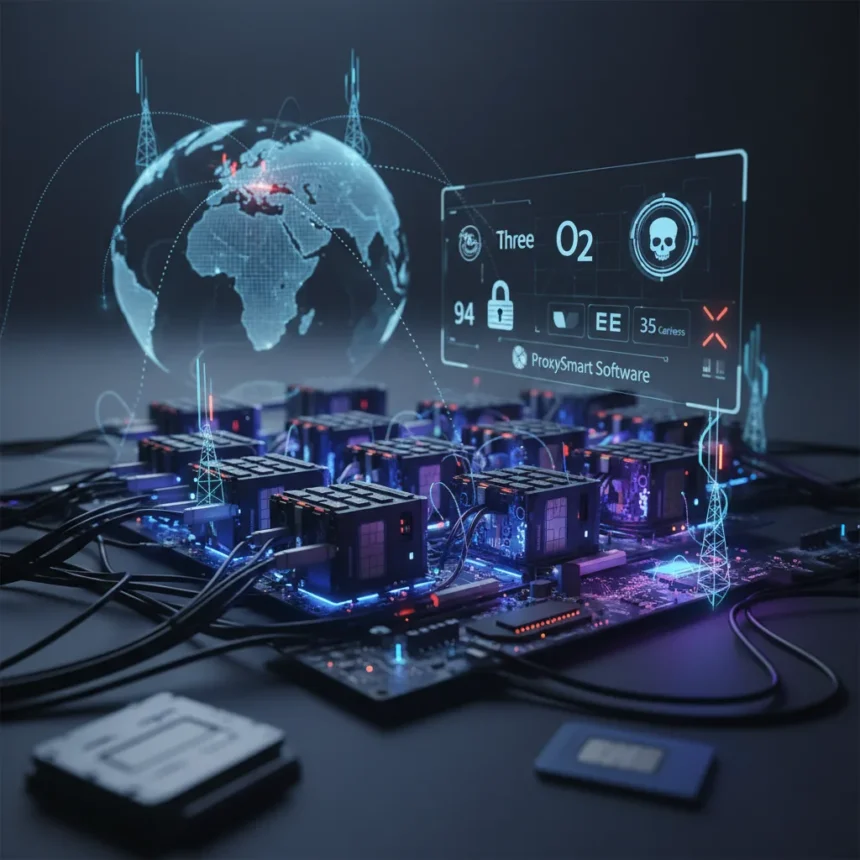
SIM farm networks refer to distributed infrastructure consisting of racks of phones, 4G/5G modems, or SIM banks that spoof mobile identities and enable account takeovers, SMS bypasses, and mass fraud. An Infrawatch investigation exposed 94 such farms across 17 countries, powered by ProxySmart, a Belarus-based software platform from Minsk that has hijacked 35 mobile carriers including major UK networks Three, O2, EE, and Vodafone.
Key Takeaways
- Infrawatch traced 94 SIM farm locations across 17 countries and 19 U.S. states, powered by ProxySmart software
- 35 cellular carriers compromised, including UK operators Three, O2, EE, and Vodafone
- ProxySmart operates 87 distinct control panels exposed across 24 commercial proxy providers globally
- SIM farms enable fraud through automated IP rotation, network fingerprint spoofing, and account creation automation
- Legal grey area allows scaling without significant disruption, according to Infrawatch CEO Lloyd Davies
How SIM farm networks compromise global carriers
SIM farm networks operate in a legal grey area that has allowed them to scale with minimal enforcement. According to Lloyd Davies, CEO at Infrawatch, “The legal grey area that SIM farms sit in has allowed that model to scale with limited disruption and we assess that it’s highly likely to be facilitating large-scale fraud operations”. These farms are typically deployed in metropolitan areas with strong 4G/5G coverage, often using external antennas to stabilize signal reception. The infrastructure is designed for remote management, enabling operators to rotate IP addresses, spoof network fingerprints, and automate account creation across social media platforms and financial services.
The ProxySmart platform provides what amounts to a “SIM-Farm-as-a-Service” model, allowing 24 different commercial proxy providers to resell access to the underlying infrastructure. One Russia-based service marketed access to U.S. SIM farms specifically, while others targeted account creation and social media automation use cases. This distributed reseller model obscures ownership and makes enforcement across multiple jurisdictions extremely difficult.
The scale of carrier compromise across continents
The Infrawatch investigation mapped 94 SIM farm locations across a staggering geographic footprint. Farms were identified in the United States, Canada, United Kingdom, Germany, Spain, Portugal, Ukraine, Latvia, France, Romania, Brazil, Ireland, Netherlands, Australia, Italy, Poland, and Georgia. Within the United States alone, deployments span 19 states including California, Texas, Maine, and Delaware, with the majority of identified farms concentrated in North America, Europe, and South America. The investigation began from a UK-based service provider and eventually traced 87 distinct control panels exposed online across 24 commercial proxy providers and the 35 compromised cellular carriers.
The choice of deployment locations is strategic. Metropolitan areas with robust 4G/5G infrastructure provide the signal strength needed for reliable SIM spoofing and account takeover operations. Some farms use external antennas to further stabilize reception, creating what amounts to a global shadow mobile network operating atop legitimate carrier infrastructure.
Why UK and US telcos remain vulnerable
Major carriers like Three, O2, EE, and Vodafone in the UK, alongside U.S. operators, have proven unable to prevent unauthorized SIM farm deployments on their networks. The vulnerability stems partly from how mobile networks authenticate devices. Traditional carrier authentication relies on IMSI (International Mobile Subscriber Identity) validation, which SIM farms can spoof through legitimate-looking SIM cards and devices. Once a farm gains foothold on a carrier’s network, it can rotate through thousands of SIM identities, making detection and blocking difficult.
The lack of coordinated enforcement across carriers and jurisdictions compounds the problem. A SIM farm operator can simply shift operations to a different carrier or country if one network begins blocking suspicious activity. Without international cooperation and standardized detection mechanisms, carriers remain in a perpetual game of whack-a-mole against distributed fraud infrastructure.
What happens now: enforcement and industry response
Recent enforcement actions signal growing pressure on SIM farm operations. The UK government implemented a landmark ban on SIM farms, and U.S. law enforcement, including the Secret Service, has seized infrastructure linked to these networks. However, the distributed nature of the ProxySmart ecosystem means that shutting down one set of control panels or farms does not eliminate the underlying platform.
The investigation’s public exposure of 87 control panels and the names of 35 compromised carriers should accelerate industry response. Carriers now have concrete evidence of which networks have been infiltrated and can audit their own authentication logs for suspicious SIM activations. Proxy service providers face reputational and legal risk for knowingly hosting ProxySmart infrastructure, creating incentive to remove the software.
Is SIM farm infrastructure still operating?
Yes. While enforcement actions have disrupted individual farms and seized some infrastructure, the ProxySmart platform itself remains operational. The distributed nature of the ecosystem—with 24 different proxy providers hosting control panels—means that removing all access points simultaneously is extremely difficult.
How do SIM farms differ from legitimate mobile proxy services?
Legitimate mobile proxy services use real devices and SIM cards to route traffic, typically for testing and quality assurance on real networks. SIM farm networks automate this process at scale for fraud, using spoofed fingerprints, rapid IP rotation, and account automation to bypass security controls designed to detect coordinated abuse. The intent and scale are fundamentally different.
What should carriers do to prevent SIM farm compromise?
Carriers should implement behavioral analysis on SIM activations, flagging patterns consistent with farm deployments: rapid activation of multiple SIM cards in the same location, unusual geographic clustering of activations, or SIM cards that activate, route traffic, then go dormant in repeating cycles. Cross-carrier intelligence sharing would help identify farms operating across multiple networks.
The SIM farm networks exposed by Infrawatch represent a critical gap in mobile carrier security. While enforcement actions and regulatory bans are beginning to disrupt operations, the underlying platform and distributed reseller model remain largely intact. Carriers that do not audit their networks for suspicious SIM patterns and implement behavioral detection are likely already compromised—they just do not know it yet.
Edited by the All Things Geek team.
Source: TechRadar