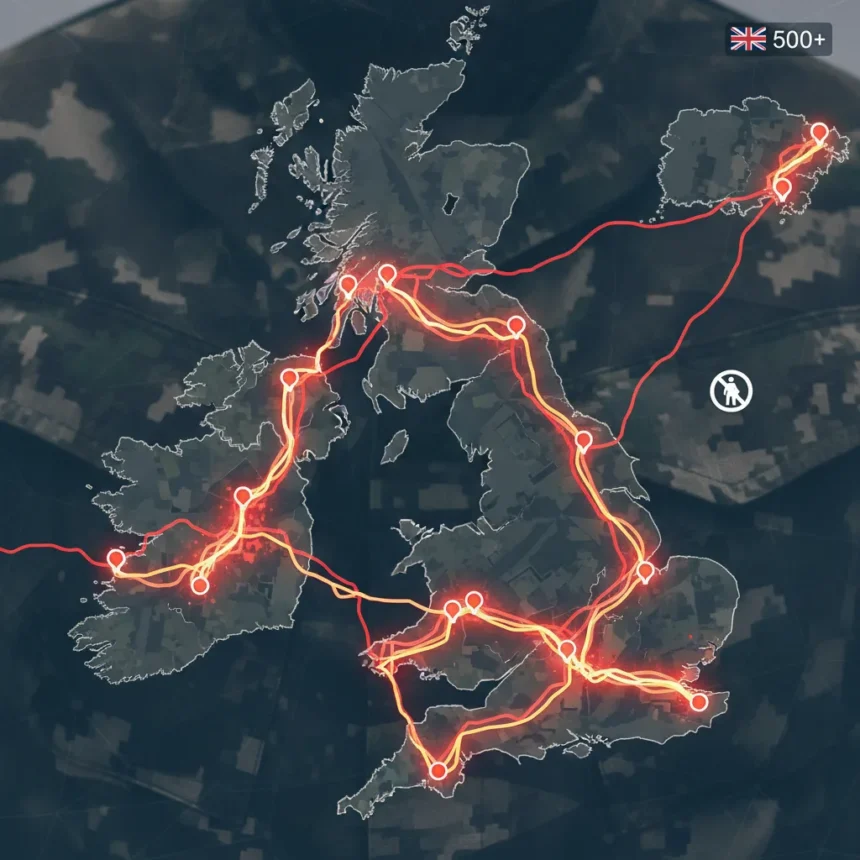
Strava military leaks are spiraling into a systemic security failure that no amount of app settings can fix. Over 500 UK soldiers have been exposed in the latest incident, their locations and activity patterns broadcast to anyone willing to look at the fitness app’s public feed. This is not a one-off mistake. It is part of a pattern spanning years, involving military personnel from multiple nations who continue to reveal sensitive operational details through the same platform.
Key Takeaways
- Over 500 UK soldiers exposed via Strava runs, marking the latest major military security breach.
- French officer revealed aircraft carrier Charles de Gaulle location 62 miles off Turkish coast via a 4.5-mile run.
- Past leaks include Macron’s bodyguards and four Biden Secret Service agents compromising locations in France.
- Strava offers privacy options to hide start/end points, but military personnel continue ignoring them.
- French armed forces acknowledged the carrier incident violated current security instructions.
How Strava Military Leaks Keep Happening
The mechanics are simple. A military officer logs a run on Strava, the app records GPS coordinates and timestamps, and the activity appears on a public profile visible to anyone worldwide. Military bases, carrier positions, patrol routes, and operational movements become searchable data points. The app’s default settings broadcast activity to the public, and many users never change them. For active military personnel, this carelessness transforms personal fitness tracking into an intelligence windfall.
The French Navy’s recent incident crystallizes the problem. A French military officer, operating under the pseudonym Arthur, posted a 4.5-mile run completed in just under 36 minutes at an average pace of 7:59 per mile. The route traced across the deck of the Charles de Gaulle aircraft carrier, revealing its exact position 62 miles off the coast of Turkey in the Mediterranean Sea. This was not a minor embarrassment. The carrier was deployed as part of French President Emmanuel Macron’s announced naval fleet deployment in March, a direct response to Middle East tensions involving the US, Israel, and Iran. The location disclosure could have compromised active military operations.
French armed forces responded with a statement to AFP confirming the incident did not comply with current security instructions. The admission reveals the core problem: instructions exist, but enforcement does not. Personnel either ignore them, do not understand them, or assume personal fitness tracking is too trivial to matter. None of these explanations excuse the breach.
Why Past Warnings Have Failed to Stop Strava Military Leaks
This is not the first time military leaders have sounded alarms. In 2024, four of Joe Biden’s Secret Service agents posted a photograph in France tied to their Strava activities, compromising their location during a protective detail. Earlier, Macron’s own bodyguards exposed his location multiple times through the app, forcing security reviews and public acknowledgment of the vulnerability. Yet the leaks continue. Training and policy statements have not translated into compliance.
The pattern suggests a generational or cultural gap. Younger military personnel grew up with social media and fitness tracking as normal, often failing to compartmentalize their digital lives from operational security. Older leadership understands the risk but struggles to enforce discipline across large, distributed forces. A single soldier ignoring a privacy setting can compromise an entire unit’s location. Strava military leaks are thus a failure of both individual judgment and institutional enforcement.
What Strava Offers to Prevent These Leaks
Strava is not entirely passive. The platform offers privacy controls specifically designed to mitigate military and security risks. Users can hide the starting and ending points of activities even on public profiles, preventing exact location disclosure while allowing the activity itself to remain visible. This feature exists precisely because Strava’s developers understood the danger. Yet it requires deliberate action. A military base security officer must actively educate personnel, and each individual must remember to enable the setting. Institutional discipline fails when either link breaks.
The existence of these controls does not absolve Strava of responsibility, but it does place the burden squarely on military organizations. They must mandate privacy settings, train personnel, and audit profiles regularly. Most militaries have not done this systematically. The result is predictable: Strava military leaks will continue until enforcement catches up to policy.
Is Strava uniquely dangerous for military personnel?
Strava is not the only fitness app, but its social features and public activity feeds make it particularly risky. Other fitness platforms offer more private-by-default designs, but Strava’s emphasis on community and competition drives the public sharing behavior that creates security vulnerabilities. Military personnel using Strava face a choice: keep the app for social motivation and accept the privacy risk, or switch to a more private alternative. Few choose the latter.
Can military personnel use Strava safely?
Yes, if they enable all available privacy controls and never post photos tied to activities. Hiding start and end points removes the location disclosure risk. Avoiding photos prevents visual identification of bases, equipment, or personnel. However, this requires constant vigilance and discipline. Most people do not maintain this level of caution indefinitely. A single lapse exposes everything.
Why don’t militaries simply ban Strava?
Banning the app entirely would eliminate the risk but face resistance from personnel who use it for genuine fitness motivation. Instead, militaries should implement mandatory training, regular audits of public profiles, and technical restrictions on app use on military networks. Until these measures become standard, Strava military leaks will remain a recurring embarrassment for defense forces worldwide.
The pattern is clear: Strava military leaks are not accidents. They are failures of security culture, enforcement, and individual discipline. Over 500 UK soldiers, a French aircraft carrier, and multiple high-level protection details have all been compromised by the same vulnerability. Until militaries treat fitness app security with the seriousness it deserves, the leaks will continue.
Where to Buy
Apple iPhone 17e | Google Pixel 10a
This article was written with AI assistance and editorially reviewed.
Source: TechRadar