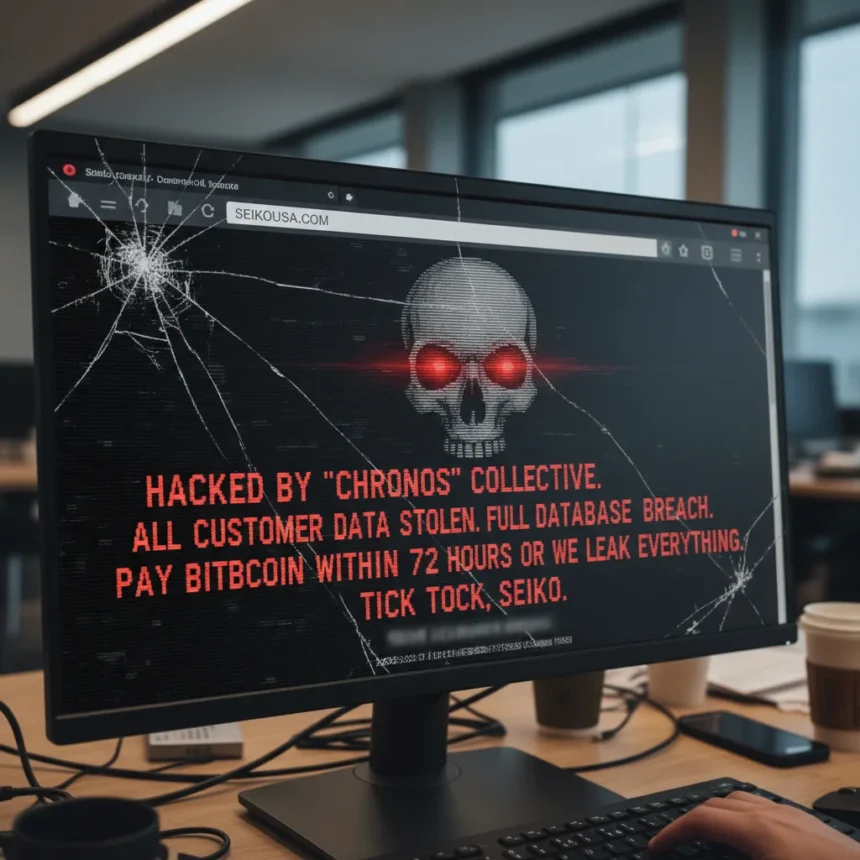
Seiko USA’s website was defaced over the weekend, with a hacker claiming to have stolen the entire customer database from the watchmaker’s Shopify backend. The Seiko USA website hacked incident marks a fresh threat to the company’s reputation, though the claims remain unverified and Seiko has offered no public response to the breach allegations.
Key Takeaways
- Seiko USA website defaced with “HACKED” message in Press Lounge section over the weekend
- Threat actor claims to have downloaded entire customer database including names, emails, phone numbers, and order history
- Attacker demands ransom negotiations via Shopify admin panel with 72-hour deadline before data release
- Seiko USA removed extortion message but has not publicly confirmed or denied the breach
- Security researchers unable to verify threat actor’s identity or the legitimacy of theft claims
What Happened to the Seiko USA Website Hacked Incident
The defacement appeared in the Press Lounge section of Seiko USA’s website, replacing legitimate content with a message reading: “This is an urgent security notification regarding your Shopify store. Your customer database has been compromised. We have successfully breached your Shopify store’s security systems and downloaded the entire customer database”. The Seiko USA website hacked page remained partially visible on the site’s review section as of the latest reports, displaying “HACKED” and “SECURITY BREACH DETECTED” messaging.
The threat actor embedded a ransom demand directly into Seiko’s Shopify admin panel, adding a contact email tied to a specific customer account ID (8069776801871) and warning that the stolen data would be publicly released within 72 hours if negotiations did not begin. This approach is unusual—rather than posting demands on dark web forums, the attacker chose to communicate directly through the compromised platform, suggesting either confidence in the breach or an attempt to maximize pressure on the company’s internal teams.
What Data Was Allegedly Stolen
According to the defacement message, the compromised dataset includes customer names, email addresses, and phone numbers. The threat actor also claims to have accessed order history containing purchase records and transaction details, along with shipping data including addresses and shipping preferences. Additionally, the attacker alleges possession of account details such as customer creation dates and internal customer notes stored in Shopify.
The scope of the alleged breach is substantial—a full customer database would expose Seiko USA’s entire client base to identity theft, phishing campaigns, and targeted fraud. However, security researchers at BleepingComputer were unable to verify the threat actor’s identity or confirm whether the data theft actually occurred. No evidence of the stolen data has surfaced on dark web forums or data leak sites, leaving open the possibility that the claims are exaggerated or fabricated.
Seiko’s Response and Unconfirmed Status
Seiko USA removed the extortion message from its website but has provided no public statement confirming or denying the breach. The company has not responded to media inquiries about the incident, leaving customers and security researchers without official clarity on whether their data was actually compromised. This silence is problematic—customers deserve transparency about whether their personal information is at risk, and delayed disclosure can undermine trust further if the breach is later confirmed.
The incident is separate from a prior ransomware attack on Seiko’s Japanese operations. In July 2023, the BlackCat/ALPHV ransomware gang confirmed stealing approximately 60,000 personal records from Seiko Group Corporation, Seiko Watch Corporation, and Seiko Instruments Inc., including employee passports and production technology. That breach had no overlap with the current USA site incident, suggesting different threat actors and attack vectors targeting different Seiko entities.
Why This Matters for Seiko Customers
If the claims are legitimate, Seiko USA customers face immediate risks. Email addresses and phone numbers are valuable for spear-phishing attacks and social engineering. Shipping addresses combined with purchase history could enable targeted theft or fraud. The 72-hour deadline creates artificial urgency, a classic extortion tactic designed to pressure companies into paying ransom without verification or negotiation.
Seiko’s silence compounds the problem. Customers cannot assess their own risk or take protective measures—changing passwords, monitoring credit cards, or filing fraud alerts—without knowing whether their data was actually taken. Public disclosure is not just a legal obligation in many jurisdictions; it is a moral one.
Is the Seiko USA website hacked claim verified?
No. Security researchers have not been able to confirm the threat actor’s identity or verify that the customer database was actually stolen. The defacement itself is real, but the claims of data theft remain unsubstantiated. No stolen data has appeared on dark web marketplaces or leak sites.
What should Seiko USA customers do?
Until Seiko issues an official statement, customers should monitor their email and phone for suspicious activity, enable two-factor authentication on any online accounts with Seiko, and consider placing a fraud alert with credit bureaus if they are concerned about identity theft. Changing passwords for accounts associated with the email address used for Seiko purchases is also prudent.
Has Seiko been hacked before?
Yes. Seiko’s Japanese operations were targeted by the BlackCat/ALPHV ransomware gang in July 2023, resulting in the theft of approximately 60,000 personal records. That breach affected Seiko Group Corporation, Seiko Watch Corporation, and Seiko Instruments Inc., but not Seiko USA’s Shopify platform.
The Seiko USA website hacked incident underscores a persistent vulnerability in e-commerce platforms: Shopify stores remain attractive targets for threat actors seeking customer data at scale. Until Seiko confirms the breach and details its response, the situation remains murky—a reminder that even established brands can struggle with cybersecurity transparency and that attackers are willing to weaponize defacement as an extortion tool. For now, the only certainty is that Seiko USA’s reputation has taken a hit, whether or not the data theft claims are real.
This article was written with AI assistance and editorially reviewed.
Source: TechRadar