The FCC router ban, enacted on March 23, 2026, represents far more than a regulatory action—it is a public admission that foreign-made consumer routers pose unacceptable national security risks to the United States. The decision should terrify any organization that has not recently audited what is actually connected to their network.
Key Takeaways
- FCC banned all foreign-produced consumer routers from new US imports effective March 23, 2026, citing national security risks.
- Foreign routers were exploited in Volt, Flax, and Salt Typhoon cyberattacks targeting critical US infrastructure and civilians.
- Virtually all consumer routers, including those from American brands, are manufactured abroad with no US-made alternatives readily available.
- Existing imported routers can still be sold and used; ban applies only to new models seeking FCC authorization.
- Enterprise and industrial routers remain exempt, but consumer-grade devices may force prolonged reliance on insecure end-of-life equipment.
What the FCC router ban actually covers
On March 23, 2026, the FCC added all foreign-produced consumer-grade routers to its Covered List under the Secure and Trusted Communications Networks Act, preventing new models from receiving equipment authorization and blocking their legal import, marketing, and sale in the US. The determination, based on a March 20, 2026 National Security Decision by an Executive Branch interagency body, cited unacceptable risks to national security, the economy, critical infrastructure, and defense. The scope is sweeping: production is defined broadly to include design, development, manufacturing, and assembly—meaning even routers assembled in the US but designed abroad fall under the restriction.
What makes this action significant is what it does not cover. Enterprise, industrial, and military routers remain exempt. Smartphones with hotspot features are not classified as routers. Most critically, routers already imported or in stock can still be sold and used. This carve-out creates a paradox: organizations may find themselves locked into aging, unsupported devices precisely when they should be upgrading to something more secure.
Why foreign routers became a national security target
The FCC router ban did not emerge from theoretical concerns. According to the agency, malicious state and non-state-sponsored cyber attackers have increasingly leveraged vulnerabilities in small and home office routers produced abroad to carry out direct attacks against American civilians and infrastructure. Specific exploits include the Volt, Flax, and Salt Typhoon cyberattacks, which targeted US infrastructure using compromised foreign-made routers. The risk extends beyond isolated incidents: routers could introduce a supply chain vulnerability capable of disrupting the US economy, critical infrastructure, and national defense.
The threat model is straightforward. A router sitting at the edge of a network, often running outdated firmware and default credentials, becomes an ideal entry point for attackers seeking to pivot deeper into organizational systems. Foreign manufacture amplifies this risk because potential backdoors embedded during production—whether through state pressure, supply chain compromise, or intentional sabotage—are nearly impossible for end users to detect or remediate.
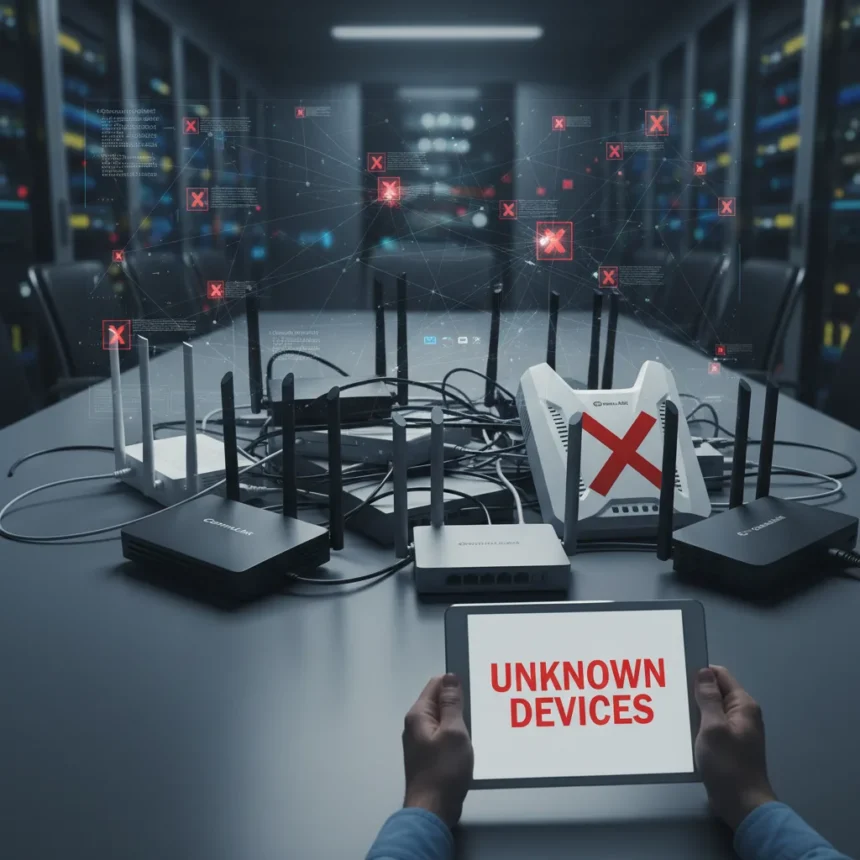
The uncomfortable reality: You probably do not know what routers you have
Here is where the FCC router ban becomes an organizational reckoning. Virtually all consumer routers, including those sold under American brand names like Netgear and TP-Link, are manufactured abroad. There are no readily available US-made alternatives. This means organizations relying on consumer-grade routers for branch offices, remote workers, or backup connectivity now face a choice: either stop importing new routers and extend the life of existing ones, or scramble to transition to enterprise-grade equipment—a costly and complex migration.
The real problem is that most organizations cannot answer a basic question: which routers are actually running on our network, where did they come from, and when was their firmware last updated? Consumer routers often ship with default administrative credentials, lack centralized management, and receive sporadic security updates. When that router is foreign-made and potentially compromised at the supply chain level, the risk becomes unacceptable.
Enterprise routers remain exempt from the FCC router ban because they are designed for professional deployment, with hardened security, remote management, and regular firmware updates. But many organizations running lean IT budgets have backfilled their networks with cheaper consumer-grade equipment. The ban forces a reckoning: either invest in proper enterprise infrastructure or accept the security liability of aging, unsupported consumer devices.
The paradox: A ban that might make home networks less secure
The FCC router ban creates a counterintuitive problem. By blocking new imports of foreign-made consumer routers, the regulation effectively forces users to hold onto existing devices longer. A router that receives no security updates is a liability, regardless of its origin. If someone is using a five-year-old foreign-made router because no new routers are available, they are arguably less secure than if they could purchase a current model from a reputable manufacturer.
This is not a reason to oppose the ban—state-sponsored backdoors are a legitimate threat—but it is a reason to acknowledge that the regulatory action alone does not solve the underlying problem. Organizations need to either transition to enterprise-grade equipment or implement network segmentation and monitoring that limits the damage a compromised router can cause. Waiting for US-made alternatives to materialize is not a viable strategy.
What organizations should do right now
The FCC router ban should trigger an immediate network audit. Document every router on your network: manufacturer, model, firmware version, and deployment date. Identify which devices are approaching end-of-life and no longer receiving security updates. For consumer-grade routers still in use, prioritize migrating critical infrastructure to enterprise-grade alternatives. For branch offices and remote workers, this may mean accelerating a shift to managed SD-WAN or cloud-based connectivity solutions that do not rely on consumer hardware.
Organizations should also inventory where consumer routers are being used as stopgaps. A router in a satellite office, a backup connection at a data center, or a device supporting guest networks may seem low-risk until an attacker uses it as an entry point. The FCC router ban is a signal that such assumptions are no longer acceptable.
Will the ban actually improve national security?
The stated intent is clear: prevent state-sponsored actors from exploiting compromised routers to attack US infrastructure and civilians. The mechanism—blocking new imports—removes one vector. But the long-term impact depends on whether organizations actually upgrade to secure alternatives or simply extend the life of existing devices. If most organizations respond to the FCC router ban by continuing to use aging consumer routers because alternatives are expensive or unavailable, the security benefit is minimal.
The ban is a necessary step, but it is not sufficient. Organizations must pair it with deliberate investment in enterprise-grade networking, regular security audits, and network segmentation that limits the blast radius if a router is compromised. The FCC router ban is a wake-up call. Whether the industry actually wakes up remains to be seen.
Does the FCC router ban apply to routers I already own?
No. The FCC router ban applies only to new models seeking equipment authorization after March 23, 2026. Routers already imported or in stock can still be sold and used. However, organizations should treat existing routers as legacy equipment and plan for replacement or isolation as part of their broader network security strategy.
Are enterprise routers affected by the FCC router ban?
Enterprise, industrial, and military routers are exempt from the FCC router ban. These devices are designed with hardened security, centralized management, and regular firmware updates, making them less vulnerable to the supply chain and backdoor risks that prompted the ban on consumer-grade equipment.
Can I still buy routers from TP-Link or Netgear after the ban?
Existing TP-Link and Netgear routers in stock can still be sold and used. However, new models manufactured abroad will not receive FCC authorization after March 23, 2026. Both companies have acknowledged the ban; TP-Link stated confidence in its supply chain security, while Netgear commended the Administration for advancing a safer digital future. Whether they will transition to US manufacturing or exit the consumer market remains unclear.
The FCC router ban is ultimately a statement about trust: foreign-made consumer routers can no longer be trusted at the network edge. Organizations that have ignored this reality for years now have no choice but to act. The question is not whether to upgrade—it is whether to upgrade now or wait until a compromised router causes a breach that forces the decision. The smart move is to audit your network today and begin planning your transition immediately.
Edited by the All Things Geek team.
Source: TechRadar