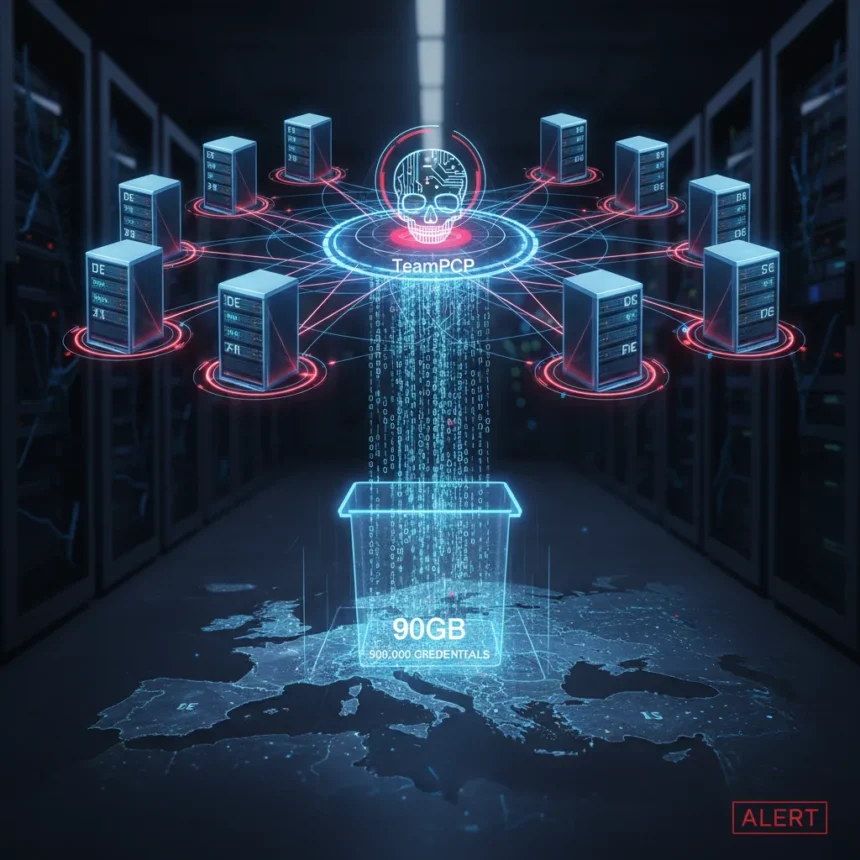
The TeamPCP supply chain attack that began in late February 2026 proved far worse than initially disclosed. CERT-EU now confirms that 30 European entities fell victim to the compromise, with 90GB of stolen data published online, revealing a breach that cascaded from Trivy through dozens of downstream tools and into over 1,000 SaaS environments.
Key Takeaways
- TeamPCP exploited incomplete credential revocation in Trivy to return on March 19, 2026, injecting malware into GitHub Actions workflows and Docker images.
- The malware stole SSH keys, cloud tokens, cryptocurrency wallets, and Kubernetes secrets while preserving Trivy’s normal vulnerability scanning function.
- Attack spread to Checkmarx, KICS, LiteLLM, and 48 additional packages within hours using harvested credentials and automated npm worms.
- Over 300GB of data exfiltrated, 500,000+ credentials stolen, with Cisco source code confirmed compromised via Trivy-linked access.
- Exposure windows lasted only 3-12 hours per component, making early detection nearly impossible for most organizations.
How the Trivy Compromise Unfolded
The attack did not begin on March 19. TeamPCP first breached Trivy’s infrastructure in late February 2026, but incomplete credential revocation left the door open for a return engagement. When the group came back on March 19 at 17:43:37 UTC, they had everything they needed. The malware injected into Trivy’s official GitHub Actions workflows—aquasecurity/trivy-action and aquasecurity/setup-trivy—overrode 76 of 77 tags in trivy-action and all 7 in setup-trivy. Docker images were similarly compromised across all available versions.
The sophistication lay in preservation, not destruction. The malware ran before the legitimate Trivy scan began, preserving the tool’s original vulnerability scanning output so victims saw no obvious signs of compromise. Behind the scenes, it dumped the Runner.Worker process memory for GitHub personal access tokens, swept 50+ filesystem paths for credentials, enumerated environment variables, and harvested cloud metadata from AWS, Azure, and GCP instances. Data was compressed and encrypted using AES-256 plus RSA-4096, then exfiltrated to typosquatted domains or a fallback GitHub repository named tpcp-docs using stolen credentials.
The Cascade: From Trivy to 1,000+ Organizations
A supply chain attack succeeds when it amplifies. TeamPCP weaponized the credentials harvested from Trivy victims to compromise downstream dependencies. Using stolen personal access tokens with write privileges, the group pushed malicious code to Checkmarx’s ast-github-action, KICS’s kics-github-action, and dozens of other widely-used repositories. Within 60 seconds, the group automated npm infections across 47 packages using pre- and post-install scripts embedded in package.json files. Similar worms deployed to PyPI and OpenVSX within 24 hours of the initial Trivy compromise.
The scale became apparent only later. Over 300GB of data was exfiltrated in total. More than 500,000 credentials—API keys, database passwords, cloud access tokens, and Kubernetes secrets—were stolen from CI/CD pipelines across victim organizations. Cisco’s source code theft via Trivy-linked credentials signaled that the breach had reached major enterprises, not just mid-market companies. By the time organizations realized Trivy was compromised, the worms had already spread to 1,000 or more SaaS environments.
The 90GB EU Data Dump and Broader Objectives
CERT-EU’s disclosure that 90GB of data from 30 European entities was published online marks a turning point in understanding the attack’s true scope. The data dump was not random. TeamPCP had clear objectives beyond credential harvesting: lateral movement into victim networks, ransomware deployment through a partnership with the group Vect, cryptomining operations, and extortion campaigns. Links to the Lapsus$ group suggest the attack was part of a broader criminal ecosystem, not an isolated incident.
The malware’s self-identification in commits—TeamPCP spoofed developer names like rauchg and DmitriyLewen—showed brazen confidence or deliberate taunting. The group left breadcrumbs. The first malicious tag v0.69.4 was pushed with timestamps that could be traced. Exfiltration infrastructure included typosquatted domains (scan.aquasecurtiy[.]org), Cloudflare Tunnels, ICP-hosted command-and-control servers, and GitHub dead drops. Every layer of the attack was designed for redundancy—if one exfiltration channel failed, another waited.
Why Detection Took So Long
The exposure window for each compromised component lasted only 3 to 12 hours. Trivy runs in thousands of CI/CD pipelines daily, often automated and unmonitored. Most organizations would not notice a malicious tag override or a Docker image update within that window. The malware preserved Trivy’s normal output, so security teams saw no warnings. GitHub Actions workflows execute in ephemeral runners that are spun up and torn down constantly—forensic evidence vanishes. By the time anyone realized something was wrong, TeamPCP had already harvested credentials and moved on to the next target.
Compared to earlier supply chain attacks like Shai-Hulud 2.0, this campaign showed evolution. Instead of corrupting a single package, TeamPCP weaponized the infrastructure of a security tool itself—the irony of stealing credentials from a vulnerability scanner is deliberate. The group understood that security tools are trusted implicitly and run with elevated privileges. Once Trivy was compromised, the malware had access to everything a developer’s machine or CI/CD environment could see.
What Organizations Should Do Now
Remediation is not straightforward. Organizations need to assume that any credentials accessed by Trivy instances between late February and March 19, 2026, are compromised. SSH keys should be rotated. Cloud access tokens should be revoked. Kubernetes secrets should be regenerated. GitHub personal access tokens should be invalidated. Database passwords should be changed. The scope is vast because Trivy runs everywhere—in development, testing, staging, and production pipelines.
The second layer is detecting lateral movement. If TeamPCP stole credentials, they likely used them. Organizations should search logs for unusual authentication patterns, new user accounts, privilege escalations, and data exfiltration in the days and weeks following the Trivy compromise. The 90GB dump from EU entities shows the group was selective—they did not publish everything, suggesting they are still actively extorting victims or preparing ransomware deployment. Paying ransoms is not recommended, but organizations should prepare for that possibility.
Is Trivy still safe to use?
Trivy itself is safe now, provided you are running a patched version from after March 19, 2026, and you have revoked all credentials that may have been exposed. The vulnerability was in Trivy’s infrastructure, not in the tool’s code. Aqua Security has since secured the GitHub Actions workflows and Docker repositories. However, trust has been broken. Organizations should monitor Trivy releases closely and consider running the tool in isolated environments with minimal credential access until confidence is fully restored.
How many organizations were actually compromised?
CERT-EU confirmed 30 EU entities with 90GB of published data, but the total reach is much larger. Analysts estimate over 1,000 SaaS environments were compromised globally through the downstream worm infections. The exact number is difficult to pin down because many organizations may not yet realize they were affected, especially if the stolen credentials have not been actively used for lateral movement or extortion.
What is the connection between TeamPCP and ransomware?
TeamPCP has a partnership with the ransomware group Vect, according to threat intelligence reports. This means stolen credentials are not just being used for extortion via data publication—they are being leveraged for actual ransomware deployment. Organizations hit by this attack should assume they are at elevated risk for encryption attacks in the coming weeks and months, even if they have not yet received an extortion demand.
The TeamPCP supply chain attack represents a new threshold in sophistication. By compromising a security tool trusted by thousands of organizations, the group gained access to credentials across an entire ecosystem in a single operation. The 90GB data dump from 30 EU entities is not the final tally—it is a warning that the attack succeeded far beyond what initial disclosures suggested. Organizations must act now to revoke exposed credentials, hunt for signs of lateral movement, and prepare for potential ransomware or extortion demands. The window for undetected compromise has closed, but the window for damage control remains open.
Edited by the All Things Geek team.
Source: TechRadar